A robust cybersecurity strategy is essential for organizations of all scales in today's shifting digital landscape. Effective deployment of this strategy promotes the protection of sensitive information.
Organizations should frequently review their cybersecurity posture and implement new defenses to address emerging threats. A comprehensive cybersecurity strategy usually covers various dimensions, such as:
* Network security|System Security
* Endpoint protection|Data Loss Prevention
* Employee training
* Incident response
Periodically reviewing the cybersecurity strategy and implementation is crucial to ensure its effectiveness in a constantly transforming threat environment.
Information Security Consulting
Navigating the complex landscape of data protection laws can be a click here daunting task for businesses. Our expert team provides comprehensive Information Security Consulting services to help you meet compliance with relevant guidelines, such as GDPR, CCPA, and HIPAA. We perform thorough security audits to identify potential vulnerabilities and develop customized mitigation strategies to protect your sensitive data. Our specialists will guide you through every step of the journey, providing clear, concise advice to help you establish a robust data protection program.
Understanding Vulnerability Assessment and Penetration Testing
Vulnerability assessments and penetration testing provide a robust approach to cybersecurity. A vulnerability assessment analyzes potential weaknesses within an organization's systems and applications, while penetration testing simulates practical attacks to exploit those vulnerabilities. This dual strategy allows organizations to mitigate the risk of cyberattacks and secure their valuable assets.
By identifying vulnerabilities before malicious actors can leverage them, organizations can implement timely remediation. Penetration testing, on the other hand, helps to validate the effectiveness of security controls and uncover any gaps in an organization's protection.
- Implementing consistent vulnerability assessments and penetration testing is crucial for maintaining a strong cybersecurity posture.
- Proficiency from qualified security professionals is essential for effective vulnerability assessment and penetration testing.
- Committing resources to these activities can generate significant returns by preventing costly cyberattacks.
Cybersecurity Education and Mock Attacks
In today's digital landscape, companies are increasingly vulnerable to advanced cyberattacks. To reduce this risk, it's crucial to invest in comprehensive security awareness training and regular phishing simulations. Security awareness training instructs employees about common risks, such as phishing emails and malware, and shows them how to identify these threats. Phishing simulations, on the other hand, are created to evaluate employee awareness in a safe setting. By simulating real-world phishing attacks, organizations can measure employee vulnerability and deliver targeted training to address these gaps.
- Periodically held security awareness training and phishing simulations are effective in improving an organization's overall cybersecurity posture.
- Employees who participate in these programs are more prepared to safeguard themselves and their organizations from cyber threats.
Incident Response Planning and Execution
Effective emergency management strategies is critical for any organization to minimize the impact of unforeseen events. A well-defined plan outlines the procedures, roles, and responsibilities in the event of an incident, ensuring a coordinated and timely countermeasure.
Crisis management groups should be trained regularly to ensure they are prepared to handle a variety of situations. The execution of an emergency action strategy involves swift assessment of the situation, clear communication with affected parties, and the implementation of pre-determined contingency plans.
Periodic reviews of the plan are essential to identify areas for improvement and ensure its effectiveness in addressing evolving risks.
Cloud Security Architecture and Governance
Implementing a robust cloud security architecture is paramount for any organization embracing cloud computing. It involves establishing a well-defined set of policies, procedures, and technologies to safeguard sensitive data, applications, and infrastructure residing in the cloud environment.
Strong governance frameworks are integral to ensuring the consistent enforcement of security standards across the organization. These frameworks provide a foundation for defining roles and responsibilities, implementing controls, and conducting regular audits and validations. A well-designed cloud security architecture should encompass multiple layers of protection, including:
* **Network Security:** Implementing firewalls, intrusion detection/prevention systems, and secure network configurations to protect the perimeter from unauthorized access.
* **Data Security:** Enforcing encryption both in transit and at rest, implementing data access controls, and adhering to industry standards for data protection.
* **Application Security:** Integrating security best practices into the application development lifecycle, conducting thorough vulnerability assessments, and implementing secure coding practices.
* **Identity and Access Management (IAM):** Establishing robust IAM policies to control user access, authenticate identities, and monitor user activities within the platform.
By adopting a holistic approach to cloud security architecture and governance, organizations can mitigate risks, protect their valuable assets, and ensure the secure and sustainable operation of their cloud-based systems.
 Mr. T Then & Now!
Mr. T Then & Now! Tatyana Ali Then & Now!
Tatyana Ali Then & Now! Amanda Bearse Then & Now!
Amanda Bearse Then & Now! Brandy Then & Now!
Brandy Then & Now!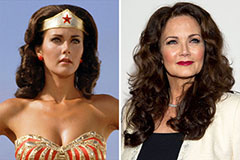 Lynda Carter Then & Now!
Lynda Carter Then & Now!